Information about Identity Management, Access Management and Federations
(Federated) Identity & Access Management
DAASI International offers comprehensive services in the field of federated Identity & Access Management (IAM). To understand federated IAM in its full complexity and to get a first impression, this page provides you with fundamental information about the three individual components: Identity Management, Access Management and Federations.
What Is Identity Management?
Identity Management (IdM) are IT systems and applications that administrate information about the identities of users – if required, completely automised.
Complexity and Risk without Identity Management
You know one or more of the following problems?
- It takes very long until a new employee gets his or her own e-mail account.
- A former employee still has access to your systems.
- You have to remember several passwords for every application or service.
- There are no or only inconvenient processes for creating a user account.
- The system administration or helpdesk is overwhelmed with the administration of the many user accounts (e.g. setting new passwords etc.)
Conventional user management stores user accounts and staff data redundantly in different databases and applications, which leads to an unecessarily high administrative workload.
If a new employee (in our example Mrs. Smith) joins an organisation without an Identity Management system, she has to contact a number of different administrative staff members or admins to be registered into various data bases and to get new accounts and access to certain resources.
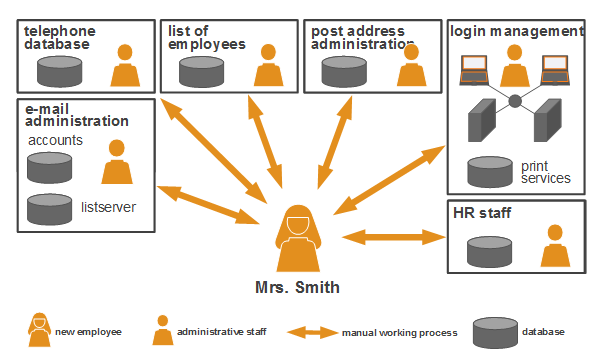
If information about Mrs. Smith changes, e.g. her position, name or address, she has to contact all admins again. When Mrs. Smith leaves the organisation, all concerned staff members will have to change the respective access rights immediately to eliminate potential security risks.
In summary, missing Identity Management leads to
- much more administration expense (and thus, more costs),
- redundant and inconsistent amount of data and
- risks in security and data privacy.
More efficiency and security with Identity Management
Identity Management uses several technologies to automatically synchronise the individual systems and databases. This often happens by a central database that is administrated in a directory service (in this case called metadirectory).
With a metadirectory, the data only have to be entered and maintained in one place. The metadirectory automatically updates and synchronises the data among all connected databases and target systems.
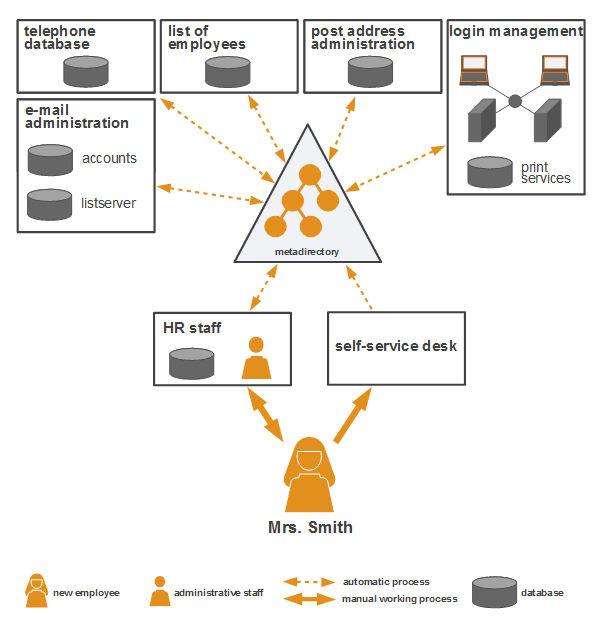
In this way, Mrs. Smith can conveniently have her data changed at a helpdesk or by the HR staff. When she is leaving the organization, some clicks are enough to securely delete her data and access rights.
Advantages: In Short, Identity Management Helps to
- Reduce Administrative Workload and Costs, and Increase Efficiency
Time is money. Due to optimised workflows the effectiveness of your staff will be increased, time will be saved, and thus costs will be reduced. - Establish Consistent Data and Data Structures, and Ensure a High Level of Security and Data Privacy
Administrating data at a central place will ensure clear structures and up-to-date data. Therefore, possible (addressing) errors will be prevented, the understanding of your systems will be facilitated, and storage capacity will be deallocated. - Increase Employee Satisfaction
Your administrative staff will be relieved by automatic and clear processes. Additionally, your employees will be thankful for only having to approach one central office, if accounts are created quickly and automatically, and if they only have to login once a day to access all necessary services.
Identity Management is recommended to all organisations which work with many identity information: universities, authorities, institutions, large-scale and midsize companies etc.
Depending on the organisation, identities are for example employees, members, guests, customers, students, or in the case of Internet of Things (IoT) and Industry 4.0 every ‘thing’ which communicates via the network.
DAASI International is experienced in working together with all organisational forms and in flexibly integrating Identity Management systems into various IT structures.
What Is Access Management?
The term Access Management comprises IT systems that administrate access to resources of all kind. Thus, Access Management is an electronically processed access control for data, computational power, software services or applications.
Access Management From an Organisational Perspective
Besides a technical implementation, organisational considerations are decisive for a successful Access Management: security relevancies and regulations, responsibilities, role concepts, data privacy etc.
Therefore, following rules should be established:
- Who has,
- to what resources,
- what access
- under which circumstances.

1. Who?
It has to be defined, which person or identity has access and how he or she can authenticate him- or herself.
A user is assigned certain attributes, group memberships or roles, which grant them the respective digital (access) rights.
Different secure methods are suitable for the authentication, e.g. passwords, X.509 certificates, hardware or SMS tokens, biometric procedures or independent values like IP addresses or IP ranges.
2. Which Resources?
The possibilities of Access Management are diverse and refer to…
- … digital resources, like data, directories, software services, applications, databases etc.
- … physical resources, like electronically secured doors, computers, hard-disc drives etc.
3. What Access?
The potential access method depends on the resource. Basically, there are different
- rights, like reading or writing permissions, and
- authorisations to run different operations, e.g. creating or deleting a user, or opening an electronically secured door.
4. Under Which Circumstances?
These rules determine further restrictions of the access rights, for example:
- Access is only possible on working days between 8 am and 6 pm.
- Access on a (text) resource is only possible, if the release date was more than 70 years ago.
- Access on an application resource (saved as an object) is only possible, if the user has not both the roles application approver and application filer (separation of duty).
- Access to the server room is only possible, if the system has not noticed a fire alarm.

Access Management From a Technical Perspective
In terms of Access Management, DAASI International mainly works with the open source technologies, didmos Authenticator, midPoint, OpenLDAP and Shibboleth, where the standards LDAP, SAML, OpenID Connect, RBAC and XACML are used.
What Are Federations?
A federation in the context of IT is an coalition of organisations based on trust. Every organisation keeps its own structure, while certain accounts, services and resources are shared with the partnered organisation(s).
Characteristics of a Federation
If two or more organizations decide to establish a federation, it is important to understand and consider following aspects:
- Every individual organisation has its own internal structure.
- The organisations occupy a position of trust, secured by contracts.
- The participating organisations agree upon standards for the data sharing.
- A central position is monitoring the compliance of the standards and and, if applicable, the creation of positions of trusts by the administration of contracts and lists of federation members and certificates of involved servers.
The Technical Aspect: Authentication and Authorisation Infrastructures
In technical terms, an IT federation is a cross-organisational Authentication and Authorisation Infrastructure (AAI).
An AAI enables users the access to services and resources of several organisations without the need to create an account for each. The user authenticates him- or herself at his or her home organisation.
A good solution for a secure authentication of the users is the OASIS standard SAML (Security Assertion Markup Language). DAASI International implements SAML with the open source technologies Shibboleth and SimpleSAMLphp, which make it possible for a user to login only once per day to authenticate him- or herself for all connected services (called Single Sign-On). Besides SAML, DAASI International also integrates other protocols and contemporary AAI technologies like OpenID Connect and OAuth2.
The user data are sent from the home organisation to the resource provider via secure communication channels, i.e. encrypted and marked with a method signature.
The biggest German IT federation is the AAI of the ‘Deutsches Forschungsnetz’ (German Research Network): DFN-AAI. DAASI International is experienced in connecting various customers to the DFN-AAI and will gladly help you in case of questions.
Learn more about the range of services of DAASI International in the field of Federated Identity & Access Management.

What Is Federated Identity & Access Management?
Federated Identity & Access Management unites all three above mentioned disciplines.
The (automised) administration of identities (Identity Management) is assisted by the security sensitive technologies of Access Management – and if requested, all that among the IT structures of several organisations (Federation).
Federated Identity Management Is Recommended If...
- … users from Organisation A should have access to resources from Organisation B.
- … Organisation B therefore does not want to create and administrate new accounts to prevent additional effort.
- … it suffices for Organisation B to have an assurance that the users are members of Organisation A.

Smooth and Productive Cooperation
Federated Identity & Access Management minimises the insecurities, frictions or contractual gaps which can occur if two or more organisations work together, and can lead to following virtues:
- Regulated structures – Uncertainty regarding the further procedures can be a major obstacle during the creation of a federation. A clear (legal) structure and process definition will regulate all succeeding steps and standards among the organisations.
- Relationship of trust – Agreed rights management ensures that cooperation partners can trust each other without reluctance, and thus can concentrate on the productive aspects of their collaboration.
- Simplification for all employees – Because the organisations keep their own IT structures, your employees do not have to be introduced to new IT systems. Additionally, they do not need to memorise further logins and passwords, because they authenticate themselves with the accounts of their home organisation. Hence, there are no reasons for your employees to disagree with the (legal and technical aspects of the) federation.

DAASI International will help you to establish a (federated) Identity & Access Management system.
DAASI International is an expert for lasting Identity & Access Management systems, and helps you to
- establish a new and strong IAM system in your organisation.
- improve, extend and optimise your existing IAM system.
- solve problems or prevent them by monitoring as a reliable support partner.
- increase security and privacy protection in your organisation.
- build a federation together with other organisations.
- integrate your organisation into an already existing federation.
- train you and your employees in IAM.
Besides open source technologies like Shibboleth, SAML, SATOSA, and OpenLDAP, DAASI International uses their own software suite didmos. Consisting of six flexible modules, didmos connects state-of-the-art open source technologies of Identity & Access Management with a strong software package, which can be fully adapted to all your needs and IT structures. Learn more about didmos here.
DAASI International works for customers from the fields of research, economy and administration, i.e. universities, research institutes, large- and medium-sized companies as well as authorities. You can find an overview of the customers of DAASI International here. Take a look here, if you would like to get more information about the services of DAASI International.
You plan to establish an Identity & Access Management system in your organisation?
Or you want to participate in a federation? DAASI International will gladly assist you in your endeavour.


