Cooperation between the Publishing House Cornelsen and DAASI International enables SCIM Interface to midPoint
The source code of the midPoint SCIM connector, as well as the overlay will be published. As open source product it is freely accessible for anyone interested.
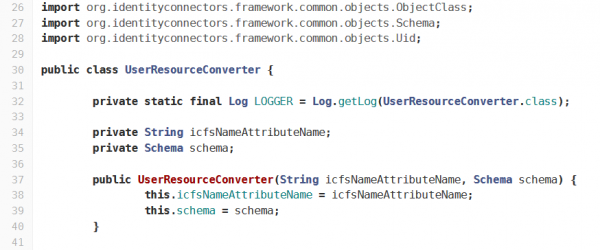
Within the means of a recent joint project of the German publishing house Cornelsen and the Tübingen-based IT service provider DAASI International, the SCIM protocol was successfully implemented into the open source software midPoint. Together, it was decided to publish the SCIM connector as well as the SCIM overlay in order to make it freely accessible to everyone. This release opens up new possibilities to quickly and easily integrate standard programmes into an existing identity and access management system (IAM system).
With recently growing popularity, SCIM (System for Cross-domain Identity Management) is set to become the standard protocol for the provision of identity data. After the successful cooperation with the publishing house Cornelsen, and their gracious agreement to publicise the source code, midPoint can now be dynamically extended via SCIM. SCIM-compatible target systems, such as Gluu, are simply provisioned by midPoint using the SCIM connector. The overlay makes it possible for SCIM-compatible clients to edit data directly in midPoint.
The cooperation with the publishing house Cornelsen was a great success,” says Peter Gietz, CEO of DAASI International, “Many companies will benefit from this integration, because with it, we can rely on one common standard instead of multiple proprietary solutions. At the same time, this also promotes acceptance for this relatively new standard.
The Community Has a Say
Evolveum, developer of midPoint, and DAASI International are discussing future support options. Until a decision has been made, DAASI International will offer support services in regard to the SCIM overlay as well as the connector to their own clients.
In case, there is a high demand for the new interface in the midPoint community, Evolveum intends to include it in the official midPoint distribution.
Interested parties can take a vote and leave a comment using the following link:
www.evolveum.com/scim-in-2020/
You can find the source code of the SCIM products here:
www.gitlab.daasi.de/midpoint/midpoint-scim-overlay
www.gitlab.daasi.de/midpoint/midpoint-gluu-client
About midPoint
midPoint is a comprehensive open source solution for identity governance and administration and is therefore often used as standard software for identity management. As an all-in-one solution and modern alternative to similar proprietary software, midPoint has all the necessary tools and configuration options necessary to introduce an IdM system – and more.
About Cornelsen
The publishing house Cornelsen is one of the leading providers of educational media in the German-speaking market. With a high level of didactic competence, employees develop products for teaching and personal learning, in print, digitally, and cross-media. The company stands for learning success and renowned high quality, which it has been providing for over 70 years. In 1946 Franz Cornelsen founded the publishing house, which has a significant influence on the German educational landscape ever since.
About DAASI International
DAASI International is an expert in (federated) identity and access management, using open source technology exclusively. Since it was founded in 2000, the IT service provider from Tübingen, Germany deals with identity management, access control and directory service technologies for universities, public authorities and companies. Additionally, DAASI International is actively involved in the field of digital humanities and participates in national and international research projects, including the digital research infrastructure DARIAH-DE. DAASI International’s range of services covers consulting, support, hosting, and software development, as well as individualised trainings.


